What Are Firewalls
Firewalls are an integral part of any secure network. As we continue the discussion of the various security features and designs, it is important to take an in-depth look at how firewalls protect a network.
3 Part : 1 - Firewalls
2 - Types of Firewalls
3 - Positioning of Firewalls
Firewalls
- Logging and notification ability
- High-volume packet inspection
- Ease of configuration
- Device security and redundancy
Logging and Notification Ability
A firewall is not much good unless it has a good logging facility. Good logging not only allows network administrators to detect if attacks are being orchestrated against their networks, but it also lets them detect if what is considered normal traffic originating from trusted users is being used for ungainly purposes. Good logging allows network administrators to filter much information based on traffic tagging and get to the stuff that really matters very quickly. Obviously, good logging is different from logging everything that happens."Good logging" also refers to notification ability. Not only do you want the firewall to log the message, but you also want it to notify the administrator when alarm conditions are detected. Notification is often done by software that sorts through the log messages generated by the firewall device. Based on the criticality of the messages, the software generates notifications in the form of pages, e-mails, or other such means to notify a network administrator. The purpose of the notification is to let the administrator make a timely modification to either the configuration or the software image of the firewall itself to decrease the threat and impact of an attack or potential attack.
High-Volume Packet Inspection
One test of a firewall is its ability to inspect a large amount of network traffic against a configured set of rules without significantly degrading network performance. How much a firewall should be able to handle varies from network to network, but with today's demanding networks, a firewall should not become a bottleneck for the network it is sitting on. It is important to keep a firewall from becoming a bottleneck in a network because of its placement in the network. Firewalls are generally placed at the periphery of a network and are the only entry point into the network. Consequently, a slowdown at this critical place in the network can slow down the entire network.Various factors can affect the speed at which a firewall processes the data passing through it. Most of the limitations are in hardware processor speed and in the optimization of software code that keeps track of the connections being established through the firewall. Another limiting factor is the availability of the various types of interface cards on the firewall. A firewall that can support Gigabit Ethernet in a Gigabit Ethernet environment is obviously more useful than one that can only do Fast Ethernet in a faster network such as Gigabit Ethernet.One thing that often helps a firewall process traffic quickly is to offload some of the work to other software. This work includes notifications, URL filter-based access control, processing of firewall logs for filtering important information, and other such functions. These often-resource-intensive functions can take up a lot of the firewall's capacity and can slow it down.Ease of Configuration
Ease of configuration includes the ability to set up the firewall quickly and to easily see configuration errors. Ease of configuration is very important in a firewall. The reason is that many network breaches that occur in spite of a firewall's being in place are not due to a bug in the firewall software or the underlying OS on which the firewall sits. They are due to an error in the firewall's configuration! Some of the "credit" for this goes to the person who configures the firewall. However, an easy-to-configure firewall mitigates many errors that might be produced in setting it up.It is important for a firewall to have a configuration utility that allows easy translation of the site security policy into the configuration. It is very useful to have a graphical representation of the network architecture as part of the configuration utility to avoid common configuration errors. Similarly, the terminology used in the configuration utility needs to be in synch with normally accepted security site topological nomenclature, such as DMZ zones, high-security zones, and low-security zones. Use of ambiguous terminology in the configuration utility can cause human error to creep in.Centralized administrative tools that allow for the simultaneous management of multiple security devices, including firewalls, are very useful for maintaining uniformly error-free configurations.Device Security and Redundancy
The security of the firewall device itself is a critical component of the overall security that a firewall can provide to a network. A firewall that is insecure itself can easily allow intruders to break in and modify the configuration to allow further access into the network. There are two main areas where a firewall needs to have strength in order to avoid issues surrounding its own security: - The security of the underlying operating system- If the firewall software runs on a separate operating system, the vulnerabilities of that operating system have the potential to become the vulnerabilities of the firewall itself. It is important to install the firewall software on an operating system known to be robust against network security threats and to keep patching the system regularly to fill any gaps that become known.
- Secure access to the firewall for administrative purposes- It is important for a firewall to have secure mechanisms available for allowing administrative access to it. Such methods can include encryption coupled with proper authentication mechanisms. Weakness in the implementation of such access mechanisms can allow the firewall to become an easy target for intrusions of various kinds.
An issue related to device security is the firewall's ability to have a redundant presence with another firewall in the network. Such redundancy allows the backup device to take up the operations of a faulty primary device. In the case of an attack on the primary device that leaves it nonoperational, redundancy also allows for continued operation of the network.Types of Firewalls
In order to gain a thorough understanding of firewall technology, it is important to understand the various types of firewalls. These various types of firewalls provide more or less the same functions that were outlined earlier. However, their methods of doing so provide differentiation in terms of performance and level of security offered.The firewalls discussed in this section are divided into five categories based on the mechanism that each uses to provide firewall functionality: - Circuit-level firewalls
- Proxy server firewalls
- Nonstateful packet filters
- Stateful packet filters
- Personal firewalls
Circuit-Level Firewalls
Proxy Server Firewalls
Nonstateful Packet Filters
Stateful Packet Filters
- Source and destination TCP and UDP port numbers
- TCP sequence numbering
- TCP flags
- TCP session state based on the RFCed TCP state machine
- UDP traffic tracking based on timers
Personal Firewalls
Positioning of Firewalls
- Topological location of the firewall- It is often a good idea to place a firewall on the periphery of a private network, as close to the final exit and initial entry point into the network as possible. The network includes any remote-access devices and VPN concentrators sitting on the its periphery. This allows the greatest number of devices on the private network to be protected by the firewall and also helps keep the boundary of the private and public network very clear. A network in which there is ambiguity as to what is public and what is private is a network waiting to be attacked.Certain situations might also warrant placing a firewall within a private network in addition to placing a firewall at the entry point. An example of such a situation is when a critical segment of the network, such as the segment housing the financial or HR servers, needs to be protected from the rest of the users on the private network.Also, in most cases firewalls should not be placed in parallel to other network devices such as routers. This can cause the firewall to be bypassed. You should also avoid any other additions to the network topology that can result in the firewall's getting bypassed.
- Accessibility and security zones- If there are servers that need to be accessed from the public network, such as Web servers, it is often a good idea to put them in a demilitarized zone (DMZ) built on the firewall rather than keep them inside the private network. The reason for this is that if these servers are on the internal network and the firewall has been asked to allow some level of access to these servers from the public network, this access opens a door for attackers. They can use this access to gain control of the servers or to stage attacks on the private network using the access holes created in the firewall. A DMZ allows publicly accessible servers to be placed in an area that is physically separate from the private network, forcing the attackers who have somehow gained control over these servers to go through the firewall again to gain access to the private network.
- Asymmetric routing- Most modern firewalls work on the concept of keeping state information for the connections made through them from the private network to the public network. This information is used to allow only the packets belonging to the legitimate connections back into the private network. Consequently, it is important that the exit and entry points of all traffic to and from the private network be through the same firewall. If this is not the case, a firewall may drop packets belonging to legitimate connections started from the internal network for which it has no state information. This scenario is known as asymmetric routing.
- Layering firewalls- In networks where a high degree of security is desired, often two or more firewalls can be deployed in series. If the first firewall fails, the second one can continue to function. This technique is often used as a safeguard against network attacks that exploit bugs in a firewall's software. If one firewall's software is vulnerable to an attack, hopefully the software of the second firewall sitting behind it will not be. Firewalls from different vendors are often used in these setups to ensure that one incorrect or compromised implementation can be backed up by the other vendor's implementation.
Summary
Ni caranye. Banyak software sebenarnye.Tapi aku guna tools ni. Belarc Advisor .
Pada aku ok laa.sebab ape info yang aku nak boleh dapat dari tools ni.
Sume info pasal laptop/pc .Leh dapat info serial number software yang kite install. security info laptop/pc kite.
sume jenis software yang ade dalam pc/laptop kite pun leh tau gak.dan byk lagi laa..leh tgk kat sini or try je download n install. BELARC
Dalam utusan ade kuar pasal pakej baru yang mantap utk ke menara petronas.
Ape yang menarik dan pakej baru tu...
" Petronas dalam satu kenyataan hari ini berkata, pakej-pakej yang akan diperkenalkan sebagai tambahan kepada lawatan sedia ada ke Skybridge di tingkat 41 itu akan turut merangkumi lawatan ke dek pemerhatian di aras teratas Menara 2, serta jamuan di Kelab Petroleum Malaysia (MPC) di bangunan yang sama. "
dipetik dari Utusan : nah ambik ni
Sejajar dengan kesungguhan untuk menjadikan menara berkembar petronas sebagai tumpuan utama pelancong dlam dan luar negara. Pi la try nanti. Aku pun tak penah melawat lebih2 petronas tu. pi isetan tu je..ekeke.
Hallu sume.
Kembali lagi Malaysia Career & Training Fair
Nah ambik link ni. byk company ade. pilih je nak mane satu.
Career yang di cari ade disini. jom jom..... MCTF10
What is ultrasurf......= ini software leh lepaskan korang dari cengkaman web filtering. Ape2 yang kene blok kat tempat koje lee.
Nak tau lebih2 bace la kat sini. aku pun ambik kat sini... UltraSurf
Bak kate Tuah ( Laksamana Hang Tuah pada zaman Kesultanan Melaka) "Takkan Melayu Hilang di Dunia"
Kata-kata negarawan terulung kita Tun Dr Mahathir " Melayu mudah lupe "
Tertarik aku dgn Utusan Malaysia keluaran 26 september 2010. " Kuasa melayu ". dengan panjang lebar dalam utusan. ( nak bace silakan Utusan Malaysia ).
Pada pemikiran aku yang biase2 je ni. Melayu memang takkan hilang didunia, tapi melayu mungkin akan hilang ape yang ade pada hari ini. Ape yang melayu ade pada hari ini adalah hanya ada KUASA. KUASA memerintah negara tercinta Malaysia. KUASA dalam menentukan hala tuju negara tercinta MALAYSIA.
Tapi tanpa disedari.Melayu mudah lupe dengan ape yang ade pada hari ini.Ape yang Melayu miliki pada hari ini. Apa yang Pemimpin melayu yang benar-benar jujur dalam memeperjuangkan KUASA dan HAK melayu.( Tak kesah la mane2 kumpulan pun)
Pada aku, PEMIMPIN Melayu skrg kene paham. Melayu tidak ade ape-ape selain KUASA. MELAYU tidak handal dalam ekonomi. Oleh itu perkasa kan Ekonomi melayu. Jagalah KUASA melayu yang ade sekarang ni, supaya tak di rampas oleh orang yang tak sepatutnye...Ade Paham. :)
Jangan bile dah terkena baru nak menyesal..... ni laa pendapat aku yang telah aku rumuskan.
Melayu takkan hilang,tapi kuase mungkin boleh hilang.
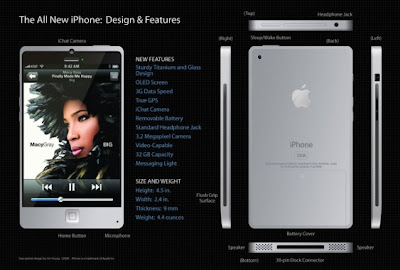
iphone 4G is coming to town......
Harga mcm gempak.. tapi tak tau laa gempak ke tak. kalu digi ade 3 plan. idigi88. idigi138. idigi238.

nak lebih2 tgk la kat website digi. iphone4G dari Digi
nah tgk ni cun ke tak. terbaik de..
Kadar pembiayaan rumah kekal 90% bak kate PM.
Bagus2. Ni memang la patut, sebab dgn ini boleh laa golongan mude yang baru2 koje ke, yang berpendapatan ok ok je boleh beli rumah.
Saya memang le bersetuju sgt2 le dgn pendekatan ni.OK laa kan untuk rumah pertama or kedua.
Kalu rumah ke3 nak wat 80% buatlee..
aku nak beli umah satu je.ehehehehehe
ehsan dari utusan online. Utusan Malaysia
This is IPS security appliance. Analyze network traffic and prevent critical threats from damaging your network.
Sourcefire provide defense from all this threat : -
|
|
|
Can protect your physical and virtual environment.
Defense you network before bad things happen.
Details.go this link.
http://www.sourcefire.com/
Halluu...
Jom register nama domain. Sape2 yang rase2 nak register name domain baru ke,nak tambah domain baru ke silalah ke sini. Aku rase macam ni je yang harge yang murah dan ok lee..
Yang ni harge tengah promosi. RM35 setahun murah tu.
Beli kat sini dapat free ni :
30 days web hosting
pre-installed WordPress
One email address
Dns hosting
Transfer of domain ownership
Ape lagi jangan sampai domain yang anda mimpi malam tadi terlepas...
details go to Webserver
Ni satu lagi....
Memang sempoi..sesempoi namanya.
Ni pun kire murah gak. RM 38 Setahun.Daftar kat sini dapat free ni :
Url forwarding
Email
Whois guard(Maklumat anda disembunyikan)free setahun je .
Nak detail2 pi la kat sini. Sempoi
Lambat register terlepas lee domain korang.
Sejauh mane keberkesanan Palo Alto ?
Ni definasi Palo Alto.
Palo Alto Networks’ next-generation firewalls provide network security by enabling enterprises to see and control applications, users, and content – not just ports, IP addresses, and packets – using three unique identification technologies: App-ID, User-ID, and Content-ID. These identification technologies, found in Palo Alto Networks' enterprise firewalls, enable enterprises to create business-relevant security policies – safely enabling organizations to adopt new applications, instead of the traditional “all-or-nothing” approach offered by traditional port-blocking firewalls used in many security infrastructures. ( http://www.paloaltonetworks.com/products/index.html )
Aku pernah pakai Palo Alto. Pada aku boleh diakatakakn user friendly laa...Senang gak nak kuar report. Tapi yang tak berkenan plak, bile masuk dalam environment network aku ade masalah lak.Box Palo Alto tu leh plak hang. Sape2 yang penah gune Palo Alto ni share2 skit. ok ke tak .Berkesan tak sebagai Firewall dalam network korang.
Ni keluarga Palo Alto.

Selanjut nye bace2 la kat website Palo Alto (http://www.paloaltonetworks.com/)
yihaaaa...
Malaysia's Largest Post Graduate Education Fair is Back.
Pot event ni kat Mid Valley Exhibition Centre.
Tarikh 8 - 10 October 2010.
Sesiape rajin atau tido je...pi la tgk.ekekek
uit...
Ceritera bermula dgn huruf B
Brocade picks Malaysia as regional centre for storage area network (SAN)
Ceritera bermula dgn huruf T
Tan Sri Muhammad Ali : I made the decision to quit JCORP
Ceritera bermula dgn huruf M
MAS Set to Receive 35 New Boeing 737-800
Ceritera bermula dgn huruf S
Seagate the first 3 Tetrabyte external desktop drive.
Ehsan dari SME & Entrepreneurship Magazine.....
Selamat bertemu lagi..
Ape tu "Business Continuity" ?
Pada saya ia adalah suatu bende atau future plan yang perlu ade untuk mane2 organisasi di dunia ini.Ini adalah untuk memastikan kejayaan sesebuah organisasi tersebut.
Semua organisasi mempunyai data yang sangat penting.lebih-lebih lagi dalam bidang " Banking","Healthcare" dan sewaktun dgnnya.
Semua organisasi didunia ini terdedah pada risiko.Sekiranya bekalan elektrik terputus,Files corrup,disaster (disaster disebabkan manusia "human-made disaster" ) (Bencana alam "Natural Disaster") dan sewaktu dgnnye.
Oleh sebab itu penting gile business continuity ni.
IT people main peranan untuk setandby dgn langkah2 sekiranya berlaku sebarang kemungkinan.
ayat lebih mudah lagi... ape2 hal pun kene buat backup. Maksudnye, kite kene identify atau kenal pasti mane data yang penting. Banyak care nak buat backup.........
Bertemu kembali...
Untuk sesiape yang belum tahu.
Sy pun baru je tahu .Busan2 mlm tadi pi la jalan2 dalam inter-net.Website ni bagus gak pada peniaga2 baru atau lame.Kecil-kecilan atau besar-besaran.Online niage or offline niage.
Yang rase baru nak mule2 niage pun ok gak. Kat website ni ade info tentang supplier.Kat ne nak ambik barang.Contohnye kerepek ke.Baju ke. Dan mcam2 lagi.
Jadinye.Pegila ke website ni jalan2.hehehe.
http://www.majalah.com
Salam dan selamat sejahtera semua.
Lame dah tak tengok2 blog aku ni. Tibe2 pagi2 ni saje2 nak buka balik.Nak tengok ape yang dah terjadi kat blog aku ni. Hah sebelum tu, SELAMAT HARI RAYA MAAF ZAHIR DAN BATIN sume.
Aku nak stat balik jage blog aku ni.huhuhh. Mungkin pas ni banyak bende2 aku akan post kan.Tungggguuuuuu.
Harap2 aku rajin laa..ekekekeke.
Selamat bertemu kembali.


 nak download kat sini
nak download kat sini